Consider this:
- Good morning! Time for coffee as you check your phone for any IM’s, reply to any you have and sit down to the New York Times. You then hit CNN and the BBC, then a weather site for your morning commute, then hit Pandora for music while you get ready for work.
- Over the holiday, you’re visiting with family. You wake up, get coffee… and check your phone for any IM’s, hit NYTimes, CNN, BBC, a weather site and then Pandora while you cook breakfast for the family (or get ready to be social). We are creatures of habit.
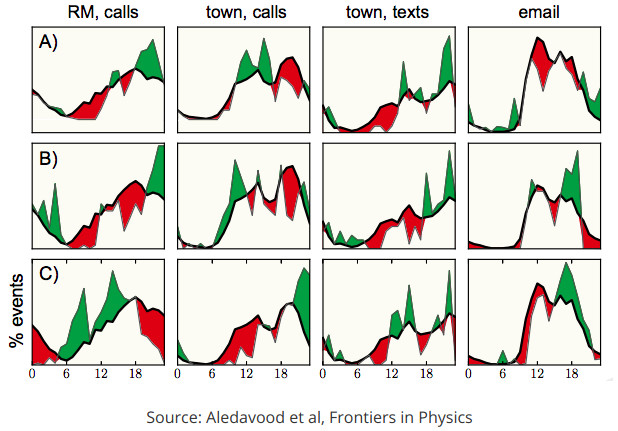
- We get up at about the same time each day, visit about the same sites and do about the same activities almost regardless of circumstances, if able.
- Metadata – information about information but not the information itself (how’s that for a definition) is not considered data by our government. In other words, When you sent an email and to whom is not the email itself, so that surrounding information is fair game for any and all analysis and by anyone.
- Therefore, anybody with access to the Internet trunk such as Verizon, AT&T, Level(3), Comcast etc, can fingerprint your activity and know where you are every day and even how you’re feeling.
- This information can be used to make money, with you – personally – as the product.
- Lastly, personal VPN’s and even TOR are useless.
The only way I know of to defeat histographic and metadata analysis is to use a spread spectrum VPN – something that “shatters” your traffic so that your activity goes out multiple, random endpoints. Even if you use a VPN to access TOR and then set an encrypted web proxy in the browser, all your activity is still going out one IP address. That’s enough to build a histogram (not to mention the advertising ID’s and other browser identifiers that cut right through those technologies).
With a spread spectrum VPN, your CNN traffic routes through LA while your NYTimes traffic comes from New York. Your PC rats you out to Microsoft from Texas. All this traffic blends in with everyone else’s, messing with their histograms and blurring yours as well.
Spread spectrum VPN’s are covered here : https://www.whisperloudly.net/projects/spreadspectrum-vpn/